
As part of a phishing campaign launched in the aftermath of Russia’s military invasion, Ukraine’s Computer Emergency Response Team (CERT-UA) has warned that Belarusian state-sponsored hackers are targeting Ukrainian military personnel and related individuals.
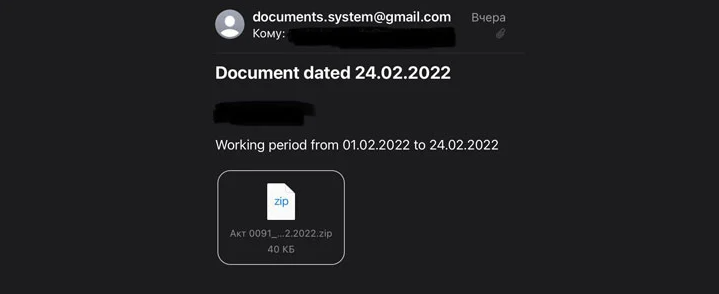
“Private ‘i.ua’ and meta.ua’ accounts of Ukrainian military personnel and related individuals have recently been targeted by mass phishing emails,” according to the CERT-UA. “Once the account is hacked, the attackers gain access to all of the messages using the IMAP protocol.”
Following that, the attacks use the victim’s address book’s contact information to spread phishing messages to other people.
The Ukrainian government blamed the attacks on UNC1151, a Minsk-based group whose “members are officers of the Ministry of Defence of the Republic of Belarus,” according to a follow-up update from the agency. The nation-state group also targets its own citizens while also targeting Russian entities, according to the agency.
- Association of Belarusians of the World (International Social Union)
- Belarusian Music Festival
- Samara Oblasna Public Organization “Russian-Belarusian Fraternity 2000”
- Dzêâslov, a Belarusian literary magazine
- Soviet Belarus (Sovetskaya Belorussiya), a daily newspaper in Belarus
- Employees of the National Academy of the Republic of Kazakhstan, and
- Voice of the Motherland, a local newspaper in Belarus
UNC1151 is the name given by Mandiant to an unclassified threat cluster that operates with goals aligned with those of the Belarusian government. Since at least 2016, the hacking group is thought to have been active.
The state-sponsored cyber-espionage group has also been linked to the Ghostwriter disinformation campaign, which spread anti-NATO and anti-corruption narratives aimed at the governments of Lithuania, Latvia, and Poland, most likely in order to undermine the governments and inflame regional tensions.
UNC1151 is also suspected of being behind the January defacement attacks on several Ukrainian government websites with threatening messages.
The Anonymous Hacking Group
The decentralized hacktivist group Anonymous tweeted, “The Anonymous collective is officially in cyberwar against the Russian government,” adding that it “leaked the database of the Russian Ministry of Defense website.”

The vigilante group GhostSec (short for Ghost Security) has also declared its allegiance to Ukraine, announcing that it has flooded Russian military websites with DDoS attacks “in support of the people in Ukraine.”

The Conti ransomware cartel, which recently acquired the now-defunct TrickBot trojan, promised “full support” to Russia and threatened “retaliation” against “anyone who decides to organize a cyber attack or any war activities against Russia.”
Later, the Conti team clarified that while “we do not ally with any government” and “condemn the ongoing war,” it “will use our full capacity to deliver retaliatory measures in the event that Western warmongers attempt to target critical infrastructure in Russia or any Russian-speaking region of the world.”
The cybercrime group RedBanditsRU and the ransomware program CoomingProject have pledged allegiance to Russia, promising to “help the Russian government if cyber-attacks and conduct against Russia occur.”




